Great Firewall of China Explained (2025): Best VPN Services Compared & Safe Multi-Device Shadowrocket Setup Guide
Explore proven ways to bypass China’s Great Firewall—VPNs, proxies, roaming SIMs, Tor bridges, and self-built servers—and learn why Shadowrocket offers the most flexible, budget-smart client setup.

This guide is part of Chinaoffbeat, a project created by travelers who love slow routes, human stories, and conversations that help you understand China beyond the obvious.
The Great Firewall (GFW), a subsystem of China’s 1998 Golden Shield Project, began full operation in 2003 to monitor and filter cross-border internet traffic.

Many major Western platforms—such as Google services, YouTube, Instagram, X (Twitter), and some news or cloud sites—are partially or fully inaccessible without approved gateways or corporate networks.
The Great Firewall blocks IPs and domains, poisons DNS responses, and uses deep packet inspection (DPI) and SNI filtering to disrupt encrypted connections—methods updated constantly.
Travelers in China generally rely on five main approaches to maintain stable online access beyond the Great Firewall:
Commercial VPN services like ExpressVPN or NordVPN offer all-in-one apps with strong encryption and easy setup, but their reliability fluctuates under frequent network updates and subscriptions are relatively costly.
International eSIM plans—for example, Airalo or Nomad—connect through offshore gateways, giving steady access without extra apps, though data is expensive and coverage can be patchy indoors.
Using a home carrier’s roaming plan (U.S. users with T-Mobile, Canadians with Bell, etc.) ensures secure, legal access through foreign networks, but roaming data costs can be prohibitively high.
Self-hosted VPN or private servers provide full control and better privacy, yet they require technical setup and can still be throttled or blocked.
Protocol-based clients like Shadowrocket let users add their own proxy subscriptions and set routing rules per app or domain—cheap, flexible, and highly customizable, though initial configuration demands some know-how and users must ensure sources and usage remain compliant.

Here are 3 VPN providers if you want quick and easy connection, without the hassle of becoming a tech savvy:
VPN | Best For | Price (approx) | Devices | GFW Success |
StrongVPN | Reliability + speed | $3.97/mo | 5 | ⭐⭐⭐⭐⭐ |
Surfshark | Unlimited devices | $2.49/mo | ∞ | ⭐⭐⭐⭐ |
PureVPN | Budget users | $1.99/mo | 10 | ⭐⭐⭐ |
What exactly Is “Bypassing the Firewall”
China’s internet operates under a nationwide filtering system commonly referred to as the “Great Firewall” (GFW). The primary purpose of this system is to monitor online activities within the country and to restrict cross-border information exchange. In the late 1990s, when China’s internet industry was still developing, the government built this firewall to manage online information flows and reduce foreign influence on the domestic digital ecosystem.

As a result, many international websites and services—such as Google, Facebook, YouTube, Twitter, Gmail, Skype, and WhatsApp—are either partially or fully inaccessible within mainland China.
To overcome these restrictions, users have adopted certain technical methods often described as “bypassing the wall” or “scientific internet access.” These tools aim to create a stable channel for users to reach overseas websites and services despite the filtering system. Such software or configurations are commonly known as “scientific internet tools” or “VPN-like applications.”
Why Free VPNs Are Not Recommended
While free VPNs may seem attractive, purely free VPN services—especially those marketed for use in China—come with significant limitations and potential risks.
First, most free VPNs are unable to bypass China’s network restrictions effectively, failing to meet users’ expectations for stable, uncensored access. Many also impose strict limits on session time, data usage, or bandwidth, making them inconvenient for consistent use.
For users who regularly rely on VPNs for work or travel, the slow speed and unreliable performance of free services are rarely sufficient. They often need more stable, efficient, and secure paid alternatives.
Worse still, some so-called “free Chinese VPNs” can expose users to security and privacy risks. Certain providers may inject advertisements, collect user data, or even disguise malware as VPN software to generate revenue. Such practices can compromise users’ personal information and online safety.
Therefore, when selecting a VPN provider, it is wiser to choose a reputable, transparent, and secure paid option. Although free VPNs may appear “cost-effective,” the privacy, stability, and security offered by a trustworthy paid service are ultimately worth the investment.
Build Your Own Proxy or Buy a Service from providers:
Bypassing the Great Firewall allows users to access websites and content otherwise restricted in China. Some people, seeking maximum speed or a clean, dedicated IP address, choose to set up their own proxy servers, often referred to as “building a ladder.”
Although many commercial VPN providers now offer dedicated IPs or private lines, these plans are typically expensive and therefore not ideal for most users.
In practice, there are multiple proxy and tunneling protocols used for bypassing restrictions—each with its own strengths, weaknesses, and technical complexity. Users interested in self-hosting should first study these protocols, then follow online guides to configure servers and clients accordingly. However, the process can be technically demanding and rarely saves much money.
Below are some of the most common protocols used today:
Shadowsocks (SS) and ShadowsocksR (SSR) – Introduced in 2012, Shadowsocks is a SOCKS5-based encrypted proxy protocol. It supports various encryption methods such as AES, Blowfish, ChaCha20, and RC4. Each request is handled independently without maintaining persistent connections, which helps conserve battery on mobile devices. ShadowsocksR builds upon SS by adding traffic obfuscation techniques, improving security, and enabling better Quality of Service (QoS) control.
V2Ray (VMess protocol) – Released later than Shadowsocks, V2Ray is a flexible framework that supports multiple proxy protocols under one platform. It requires both a client and a server. Users can rent their own virtual servers to host V2Ray or purchase ready-made V2Ray nodes from service providers.
Trojan protocol – Despite sharing its name with the well-known “Trojan horse,” this is not malware. Unlike Shadowsocks, Trojan does not rely on custom encryption schemes but instead uses the TLS (HTTPS) protocol to disguise traffic, making it appear like ordinary encrypted web activity. Trojan enforces TLS by design, meaning a valid domain name is required to deploy it. In terms of performance, it offers speeds similar to V2Ray while consuming fewer server resources—allowing even low-spec servers to run smoothly.
Why Shadowrocket (SSR) Is Widely Used
Among the various proxy and tunneling tools available today, Shadowrocket, which commonly relies on the ShadowsocksR (SSR) protocol, has become one of the most widely used solutions among Chinese users. Its appeal lies in a combination of affordability, flexibility, and broad device compatibility.
Shadowrocket supports multiple platforms—including iOS, Android, Windows, macOS, Apple TV, and even routers—allowing users to set up network-wide routing with a single configuration. Compared with traditional VPNs, SSR connections are usually cheaper and easier to customize, making them popular among users who prioritize cost efficiency and access convenience.
However, it is not the most secure option. Because configurations often depend on third-party servers and manually supplied subscriptions, data privacy and legal compliance risks can vary. Users should carefully assess these factors before use, ensuring that their setup aligns with local laws, privacy requirements, and personal risk tolerance.
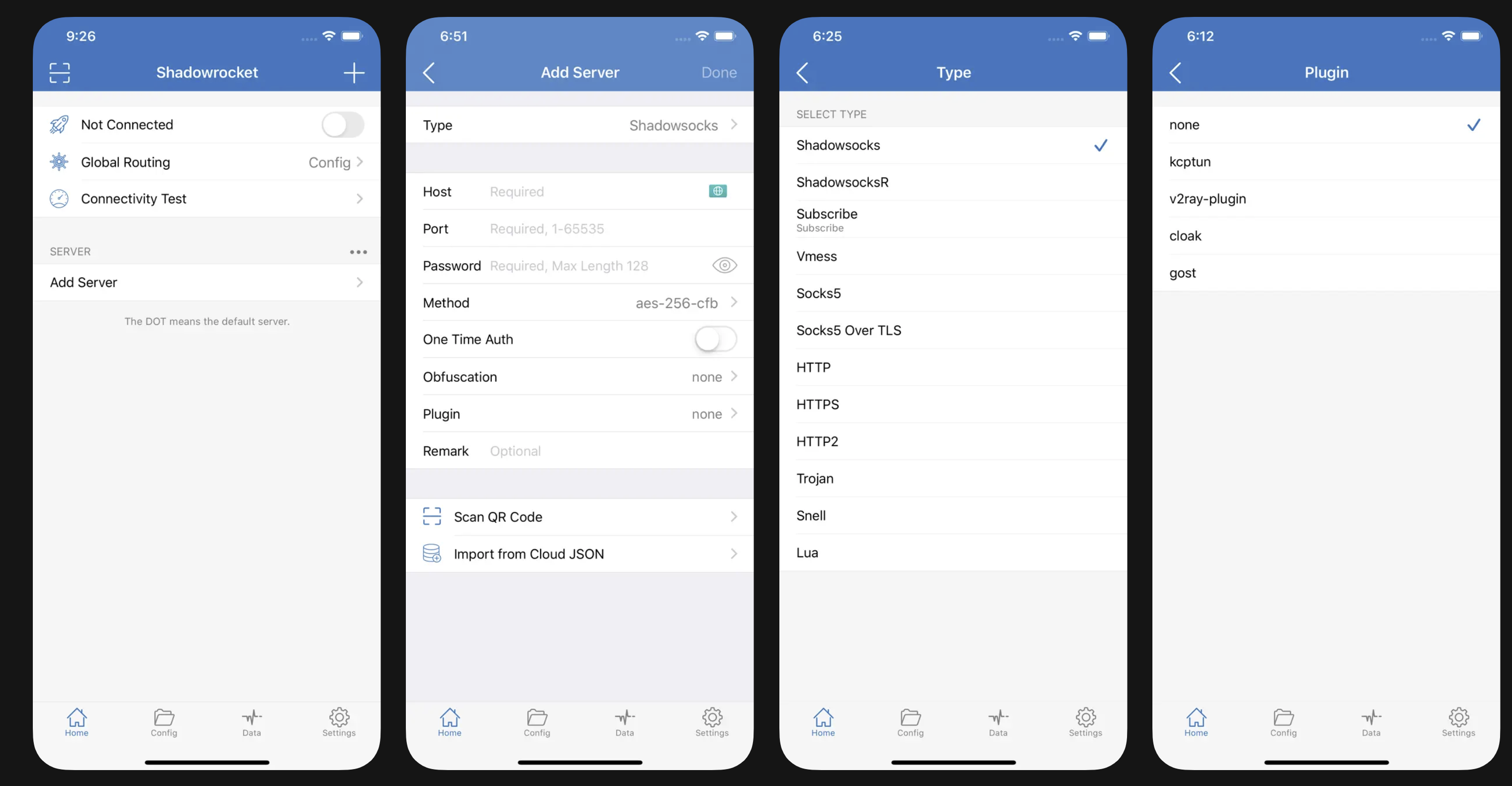
Shadowrocket, available on the App Store for US $3.99, supports the ShadowsocksR (SSR) protocol across Apple devices. Be sure to buy the genuine app—there are knock-off copies under similar names.
The app itself is only a client, not a service provider. To connect, you’ll need a VPS (Virtual Private Server) or proxy subscription from an external vendor, which supplies the actual network route. Shadowrocket simply applies your settings to encrypt and direct traffic.
Because SSR setups are flexible, many allow multiple devices under one account, making it easy to share bandwidth with family or friends. Just remember that performance, legality, and privacy all depend on your chosen provider and how you use it.

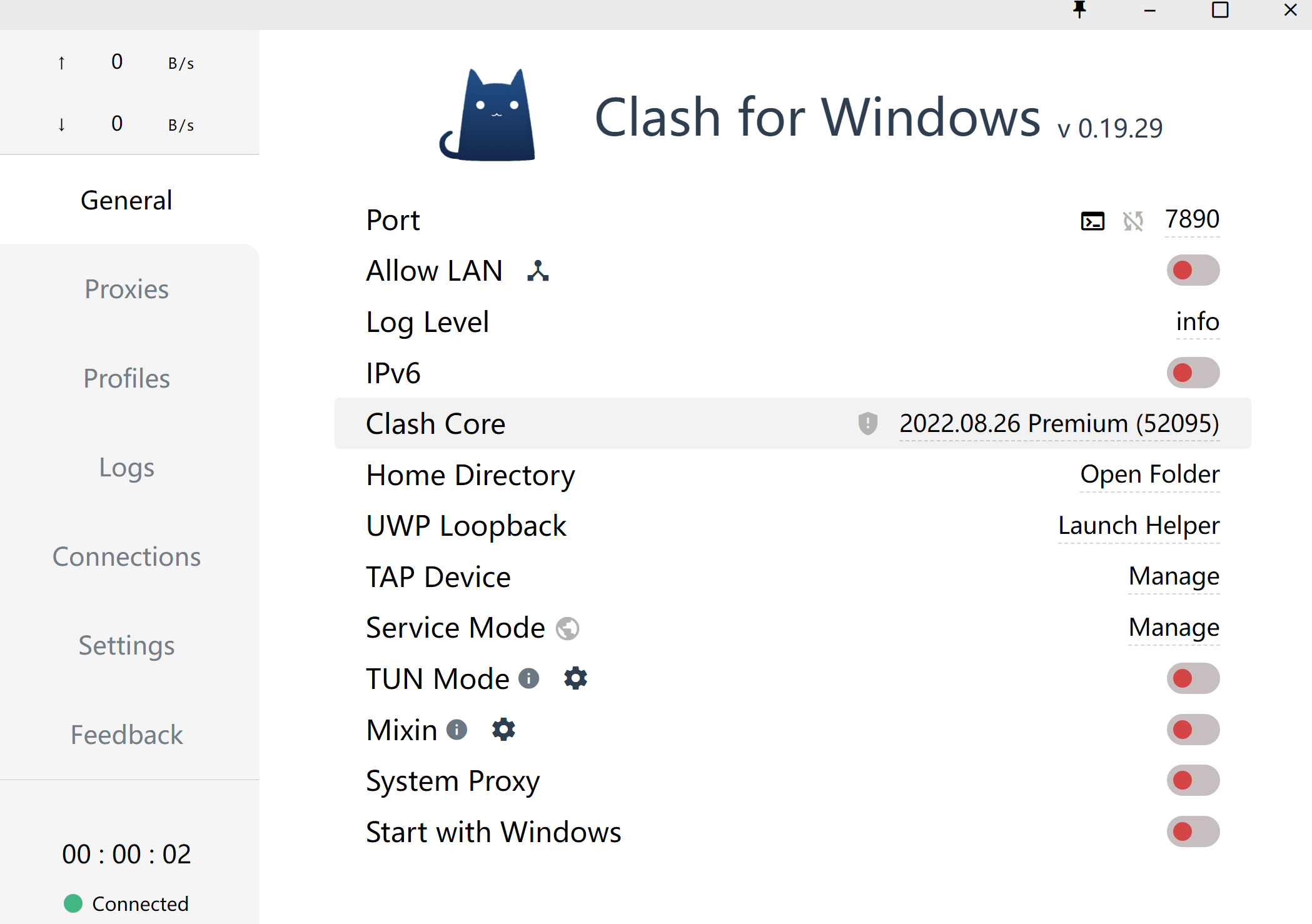
Clash for Windows--Deploy SSR on your PC quickly
Download Clash for Windows, an open-source, free SSR application to install on your PC.
Shadowrocket for AppleTV--Unlock Full Western Streaming Experience
Read the full instructions on how to install and set up your Shadowrocket on your AppleTV

Related blog posts

How to Find Authentic Restaurants in China: A Practical Guide for Travelers
From download to booking: step-by-step instructions for using Dianping (大众点评) to pick the right city, switch to English, filter by cuisine and ratings to eat where locals actually go.

Best Authentic Peking Duck in Beijing (2025): 4 Classic Restaurants and the History Behind the Dish
Taste Beijing’s signature dish where it all began. Discover the 1,000-year history of Peking Duck and the four restaurants that still roast it the traditional way — crisp skin, tender meat, and centuries of craft.

